Why Journalism Matters
Investigations into China's plan to rule the world and North Korea's 'fake' IT workers infiltrating global business. Plus praise for the whistleblower fighting to clean up Britain's dirty rivers
4 minutes read
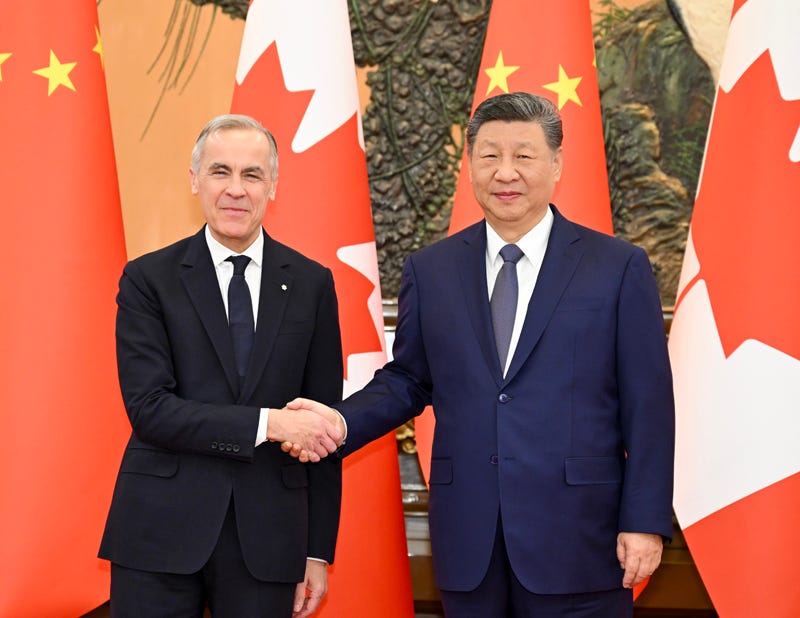
Investigating how China seeks to undermine the west, with Canada a key target
“Entice the enemy’s best and wisest men, so that he may be left without counsellors. Introduce traitors into his country, that government policy may be rendered futile. Foment intrigue and deceit, and thus sow dissension between the ruler and his ministers.”
—Sun Tzu The Art of War
Currently, the headlines are dominated by the war initiated by America and Israel against Iran. As the war moves into its second week its impact is widening with countries from Kuwait to Cyprus to Saudi Arabia sustaining attacks from the Iranians. There’s also been a great surge in oil and gas prices, following the a virtual shutting down of all the shipping transiting the vital Straits of Hormuz in the Persian Gulf .
This is affecting world trade, particularly for China which imports as much as 40 percent of its oil and 30 percent of its liquid natural gas (LNG) through the strait. Beijing has publicly urged all parties in the war to keep the strait open to avoid disrupting international trade.
And while the world is focussed on the wars in the Middle East and Ukraine on the other side of the Eurasian continent, the world’s preeminent superpower-in-waiting is biding its time while continuing to burrow into the life and political institutions of western democracies.
Recent research and investigation show that China has ideas of its own about how the world should be run.
WJM has frequently reported on recent work carried out by The Bureau, the Canadian investigative outlet produced by award-winning reporter Sam Cooper. He specialises in coverage of the ongoing threat posed to the west from the Communist Party regime in China.
Beijing’s prototype
As Cooper reports from Ottawa: “ In the wake of a groundbreaking Jamestown Foundation study mapping 2,294 CCP-linked organisations across four Western democracies — and finding that Canada, with 575 such groups, has nearly five times the per-capita penetration rate of the United States — experts including a former Chinese spy who defected to Australia are warning that Canada has become Beijing’s prototype for the kind of subversion that, in CCP doctrine, precedes kinetic warfare.”
Cooper cites detailed research produced by the American Jamestown Foundation, an American think tank based in Washington. The Jamestown specialises in analyzing strategic threats to American national security.
As Cooper explains: “The Jamestown research, led by analyst Cheryl Yu under the guidance of former CIA China expert Peter Mattis, exposes a sophisticated system designed to steal sensitive technology, launder money, smuggle migrants, monitor and control diaspora communities, and advance Beijing’s ultimate strategic objective: displacing the United States as the dominant global power.
Critical platform
“Canada, the data suggests, has become a critical platform in that effort — not despite its closeness to the United States, but because of it.”
Also contributing to the Jamestown report is a former spy who defected to Australia in 2023. Known only as “Eric” this agent worked for Office No. 1 of China’s Ministry of Public Security from 2008 until 2022.
Eric told the Epoch Times that Canada remains a “key target” for CCP infiltration because of its “ relatively lenient immigration policies, less robust counterintelligence infrastructure compared to the United States, and its valuable membership in the Five Eyes intelligence alliance.
“Because it is safer to enter and exit the U.S. from Canadian soil, Eric explains, the CCP frequently uses Canada as a staging ground to access sensitive allied data while bypassing America’s stricter counterespionage scrutiny.
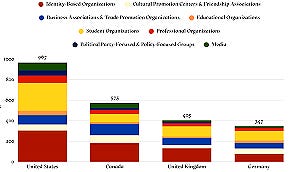
The Chinese government often works through the thousands of overseas Chinese organisations that operate around the world, very often without hindrance or surveillance. These are tied to the increasingly powerful United Front Work Department.
United Front
This department is the official locus for China’s attempt to undermine opposition at home and spread influence abroad.
As the Bureau explains: “The United Front is a series of stratagems directed by the CCP and implemented by swarms of agents and moles — often masquerading as dissidents, journalists, researchers, academics, interns, maids, nannies, and chauffeurs — to gather information, but far more critically, to spread disinformation.”
The United Front approach involves ‘elite capture’ which means co-opting influential figures—from prime ministers to intellectuals to corporate leaders as well as gaining traction in multilateral institutions, government bodies and universities.
As The Bureau explains: “China’s subversion of the World Health Organisation to conceal its responsibility for the COVID-19 pandemic, the influence of its Confucius Institutes, and the co-option of numerous Western figures stand as prominent examples.”
The endgame for China? To become the most powerful nation in the world supported by vast economic resources and the world’s second strongest military.
As The James Foundation concludes: “Understanding the United Front is no longer optional.”
Reference
James Foundation: Mapping China’s United Front overseas influence
4 minute read
Tales of cybercrime: Investigating North Korea’s global fake IT workers

As the working world continues to embrace wholeheartedly advanced cybertechnologies, the gap between science fiction and present-day reality seems to have completely disappeared.
The futuristic is futuristic no longer, particularly in the latest developments in cyberespionage. And though the threats to our wealth and well being are not particularly new, media investigations have revealed that the latest criminal actions have already impacted some of the leading companies in the west.
And North Korea—once cut off from the wider world and dismissed as a cartoonish grotesque among ‘developing’ nations— is now at the centre of cyber skullduggery, adding to the threats posed by its acquisition and advances in nuclear weapons.
Welcome to Cyberscoop, viewed as one of the leading editorial outlets specialising in cybersecurity. Over the last couple of years they have been following the expanding saga of North Korean nationals infiltrating the IT departments of top global companies by using AI to create false identities for themselves, including changing their voices and cloning facial images that make them appear to be American computer experts.
Mandiant is a leading cybersecurity company, now part of Google Cloud. Their Chief Technology Officer Charles Carmakal sounded the warning at a major digital security conference last year in San Francisco.
He said: “There are hundreds of Fortune 500 organisations that have [unwittingly] hired these North Korean IT workers.”
Fortune 500
“Literally every Fortune 500 company has at least dozens, if not hundreds, of applications for North Korean IT workers. Nearly every CISO that I’ve spoken to about the North Korean IT worker problem has admitted they’ve hired at least one North Korean IT worker, if not a dozen or a few dozen.”
Even Google, which ranks eighth on the annual list of the top global companies by revenue, has been caught up in problem.
Although Google does not believe it has hired any North Korean technical workers they have been detected among job candidates and applicants according to Iain Mulholland, senior director of security engineering at Google Cloud.
Mulholland is unambiguous about the escalating scale of the threat, warning companies that they should assume that North Koreans are actively targeting them.
He told Cyberscoop that “If you’re not seeing this, it’s because you’re not detecting it, not because it’s not happening to you.”
Some of these remote IT workers are based in Korea, some elsewhere, most probably over the border in China. Once hired by international companies they deploy elaborate strategies to hide their identity and their location. To a large extent the threat has grown with the explosive advent of remote working around the world since the Covid pandemic.
Some estimates put the income earned by these fake workers at between $USD250 million and $600 million annually. The workers themselves often keep only 10 per cent of their earnings with 90% going back to Pyongyang and put to use in support of illicit weapons programmes.
Although these threats can come from anywhere in the world it appears that the preponderance of the activity centres on North Korea as it attempts to circumvent UN sanctions.
AI generated
The scam typically involves the state training and grooming these fraudsters to apply for remote work in the west, using AI-generated fake identities and the help of “facilitators” in the country where the targeted company is located.
In a report in the Guardian in early March Guy Milmo, Global Technology Editor examined Microsoft’s experience with North Korean infiltration.
Milmo wrote: “Microsoft listed a number of AI-related scams in use by North Korean groups, called Jasper Sleet and Coral Sleet in line with the convention of cybersecurity analysts giving monikers to unnamed clusters of assailants.
“The tech company said the scammers had used voice-changing software during remote interviews to mask their accents, allowing them to pass as western candidates. They also use the AI app Face Swap to insert the faces of North Korean IT workers into stolen identity documents and to generate ‘polished’ headshots for CVs.
“Jasper Sleet leverages AI across the attack lifecycle to get hired, stay hired, and misuse access at scale,” Microsoft said.
“Last year, Microsoft said it had disrupted 3,000 Microsoft Outlook or Hotmail accounts used by fake North Korean IT workers.”

Ironically, even firms specialising in cybersecurity are not immune from being infiltrated. In 2024 Cyberscoop, one of the leading cybersecurity training firms, KnowBe4, admitted it had been targeted.
The company said it was quickly able to isolate the threat and then went to the FBI and Mandiant who concluded the worker was a ‘fictional persona’ operating from North Korea.
Plant malware
Once inside, the fake workers then use AI to write emails, translate documents and generate code or plant malware which could be triggered at some time in the future using a ‘backdoor’ constructed by the North Korean agent.
“The scam is that they are actually doing the work, getting paid well, and give a large amount to North Korea to fund their illegal programmes,” Stu Sjouwerman founder and executive chairman of KnowBe4 wrote. “I don’t have to tell you about the severe risk of this.”
Reference
4 minute read
Whistleblowers and campaigners are the heroes in the battle to reveal the dangers of water pollution in the UK

In assessing the impact of investigative journalism it’s impossible to overemphasise the importance of whistle blowers and civil campaigners . They often play a crucial role in revealing important undisclosed information that often holds the key to our continued well being and the survival of democratic accountability.
They also do so at considerable cost to themselves, putting their lives, careers and families on the line without any expectation of recompense or recognition.
Yes, there may be hidden agendas for some of them, but if their efforts are judged simply by how well they serve the public interest, then commendation is well deserved.
So today, in the UK, it is time to praise Robert Forrester, an engineer who worked for the country’s Environmental Agency monitoring the quality of the UK’s water supply and trying to enforce the laws and regulations which are meant to keep water clean, secure, and safe to drink.
Downgraded incidents
Because of his Freedom of Information requests and leaks to the media, the public has learned that over many years the country’s Environment Agency (EA) downgraded thousands of serious pollution incidents in English rivers by private water companies without even paying visits to investigate.
Forrester has only been able to identify himself since January when he agreed to leave the agency. He had been recognised by his employers as the source of leaked information in 2021 when he was suspended and put on restricted duties. He believed he was being victimised as a whistleblower and eventually reached a settlement with the agency before his recent departure. It is not known what he is doing for a living now.
He has been shining a light on the water industry for nine years with his work highlighted in a recent widely seen TV docudrama Dirty Business. He has vowed to go on exposing the truth about the state of water pollution across Britain.
According to a very recent report in the Guardian by environment correspondent Sandra Laville FOI data shows 2,778 serious pollution incidents by water companies were reported in 2024. Of these, 2,735 (98%) were downgraded to minor incidents by officials. Officers only attended 496 of these before downgrading the pollution event. The data released indicates the rest were deemed minor events on water company evidence alone.

“There is a significant increase in the serious incidents received by the agency but a huge increase in them being downgraded with no attendance by an officer,” Forrester told the newspaper.
“The key thing is that water companies are still controlling our attendance. As an officer with 21 years’ experience I saw it change from 12 to 15 years ago when we would actually get out on site, and we were encouraged to protect, investigate and enforce.”
Forrester began leaking information to reporters and Greenpeace in 2017. In their Unearthed investigative outlet Greenpeace began reporting about toxic sludge being spread on farmland without sufficient oversight by the EA.
According to the Guardian ‘for the 2025-26 financial year, the EA expects to receive approximately £149m in income from water companies through permit charges and a new enforcement levy, out of a £189m total budget for water regulation’.
“But Forrester said this model of water companies paying for the budget of agency enforcers created a conflict of interest.
“The regulator is in too close a relationship with the water companies. They are being funded from the money the water companies pay for their permits and as a result the regulator appears to be loosening its regulatory hold over them.”
Pumped into a sewer
According to an interview with The Times Forrester said the tipping point for him was an incident in West Lancashire in 2017, when industrial waste was pumped into a sewer.
“It entered the groundwater, causing severe surface water pollution in the nearby river but also melted the drinking water pipe of the next door property. People there were drinking carcinogens for two to three weeks at about 1,000 times the human health limits,” he claims.
The report added:“Despite the agency categorising this as a ‘category one’ incident — the most serious level of environmental impact — no enforcement action was taken. Forrester thinks the investigation stalled because of “limited money,” he says.”
The Environment Agency claims to have cleaned up its act and is critical of how it is portrayed in Dirty Business. A spokesman told The Times: “The depiction of the Environment Agency in this film does not reflect the significant changes the organisation has undergone in recent years to better tackle water pollution, which we take extremely seriously.
“More people, better data and increased powers mean we will always act on intelligence of potential offences. This year we are on track to do 10,000 inspections of water company assets, rooting out wrongdoing and driving better performance.”
Reference
Times report on Robert Forrester
Guardian report on Environment agency
Greenpeace investigation of toxic sludge
It’s free to subscribe and you can cancel any time, so give it a try!
Contact us on greatjournalismwjm@gmail.com
Follow us on Facebook
facebook.com/whyjournalism matters



